Active Directory Token Bloat
What is Token Bloat?
Token Bloat is one of the major problems faced by IT administrators,
which occurs when a single user is a member of too many groups in Active
Directory. In a large organization there is an ocean of Active Directory
resource like users, groups, computers etc. Each user is required to
play a unique role in the organization, so it’s the IT administrators’
responsibility to assign sufficient permissions to the user to access
the services and applications necessary to perform his/her task. At the
same time IT administrators are required to maintain the security
standards of their organization. As a result their job becomes more
complex and granular in providing and denying specific permissions to
each user. Moreover it is unavoidable to add a user as a member to
multiple security groups to assign permissions. This results in stuffing
of security groups or SID History items into a user token, which in turn
increases the Kerberos Token Size above the default size of 20000 bytes.
What are the Symptoms for Token Bloat?
Based on the number of groups a single user is memberOf, the intensity
of Token Bloat varies as follows,
According to this KB
Article , for an
user account who is a member of more than 100 groups,
“When you try to connect to a Microsoft Internet Information Server
(IIS) computer that is configured to use Microsoft Windows 2000
authentication, you receive an Enter Network Password dialog box. When
you try to log on, you may be prompted to provide your network
credentials again, and after you do so, you may receive the following
error message:
You are not authorized to view this page
You do not have permission to view this directory or page using the
credentials you supplied.”
According to this KB
Article ,
for an user account who is a member of 1,015 groups,
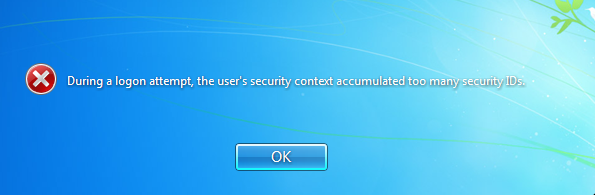
“When a user tries to log on to a computer by using a local computer
account or a domain user account, the logon request may fail with the
following error message:
Logon Message: The system cannot log you on due to the following error:
During a logon attempt, the user’s security context accumulated too many
security IDs. Please try again or consult your system administrator.”
The screenshot given below is generated during logon of a user (member
of 1200 groups) in the test lab,
What are the Causes for Token Bloat?
- Users Migration from one domain to other including SID History to
preserve access to resources for the user. - User added as member to many security groups and those groups are
nested into other group memberships.
How to Prevent Token Bloat?
The only way to prevent token bloat is to reduce the number of group
membership for users.
Dynamic Access Control
Dynamic Access Control considerably reduces the complexity of a
combinatorial number of security groups, so that you can have a clear
understanding of who can access what data and you are able to easily
adjust access when people move between different roles in the company.
Effect of Nested-Group Model on Token Bloat
Nested AD groups does not solve the token bloat issue, instead it makes
it worse. If you look at a user in Active Directory, and look at the
“Member Of” tab, you’ll only see the short list of transitive role-based
groups. But you will not be able to see the intransitive groups that are
nested as members of role-based groups. However, the user’s Kerberos
token will contain both, thus making token bloat much worse.
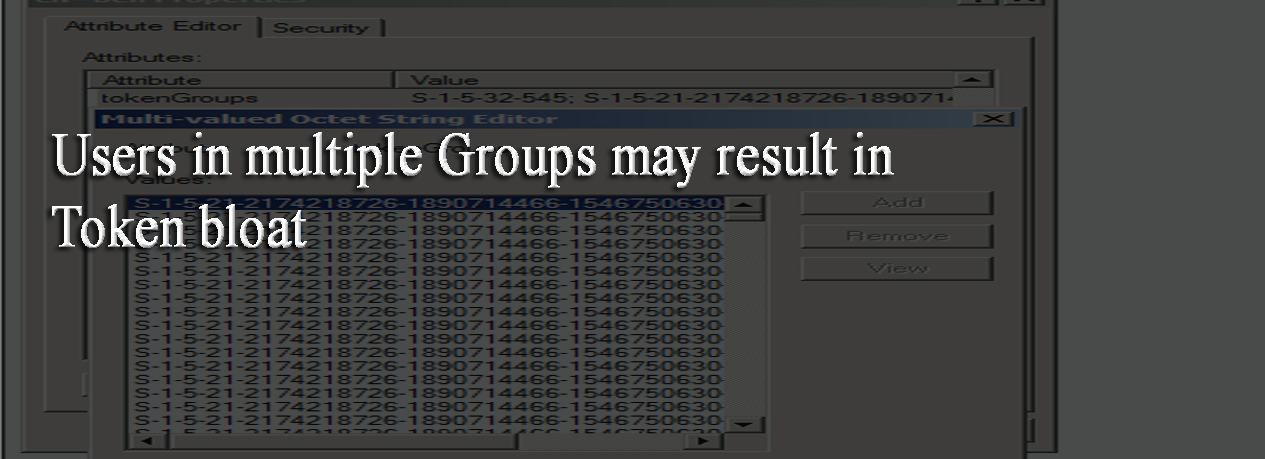
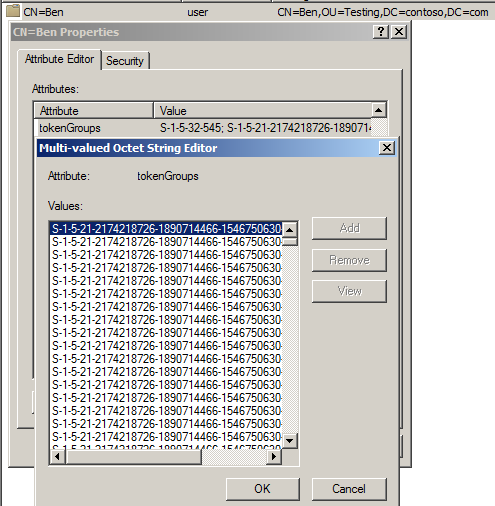
Kerberos token gets the SIDs for the groups the Active Directory users
belongs to from the tokenGroups attribute. The screenshot given below is
on test user – Ben’s membership to the list of SIDs of groups from
ADSIEDIT,
How to Fix Token Bloat?
By overriding the default value of “MaxTokenSize” registry entry, which
is located under
SystemCurrentControlSetControlLsaKerberosParameters, you
can avoid the token bloat error during the login. The default value of
this registry entry is 20000, but by starting Windows Server 2012, this
value is set with 48000 bytes by default. This
blog
explains better about “MaxTokenSize” improvements in Windows Server
2012.